Recent Blog Posts
Wardriving 2024: Using Electricity Meter Readers to Get In
Do you pentest IoT equipment before joining it to your network? I did, fortunately. I bought a Swedish reader to connect to the P1 port of my electricity meter, and found a number of vulnerabilities that in combination let an attacker “wardriving” outside my house use the P1 reader to join my Wi-Fi network!
So it’s true what they say: the S in IoT stands for Security! ;)
The Akamai Origin Disclosure Non-vulnerability
When working for my employer Sentor I discovered an origin disclosure vulnerability in Akamai GTM, but they didn’t agree it was a vulnerability. I blogged about it on the company blog: The Akamai origin disclosure non-vulnerability
read more
Vulnerability Disclosure: Authentication Bypass in Auth0
When working for my employer Sentor I discovered an authentication bypass vulnerability in Auth0. I blogged about it on the company blog: Vulnerability disclosure: Authentication bypass in Auth0
read more
Vulnerability Disclosure: Session Fixation in Auth0
When working for my employer Sentor I discovered a session fixation vulnerability in Auth0. I blogged about it on the company blog: Vulnerability disclosure: Session fixation in Auth0
read more
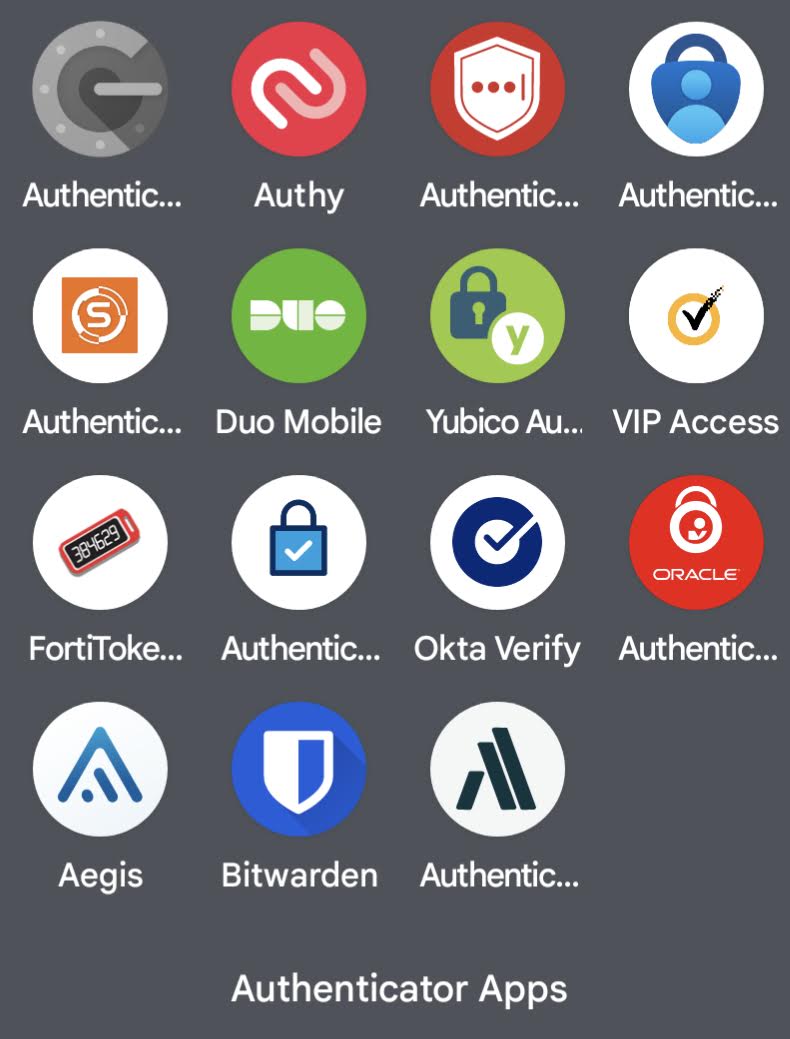
Mobile Authenticator Apps Algorithm Support Review - 2023 Edition
Last week my favorite IT security podcast Bli säker (Become Secure in English) published the episode The Epochalypse and the QR Code (only in Swedish) where they explained the techonology behind mobile authenticator apps. I felt I needed to refresh my TOTP algorithm support investigation from 2019 before the recording of the next episode of the Bli säker podcast. :)
So this is an update to the blog post I published in July 2019 called Many Common Mobile Authenticator Apps Accept QR Codes for Modes They Don’t Support.
read more